SENTINEL COMMAND CENTER
Protects your business assets via Centralized Security Command Center
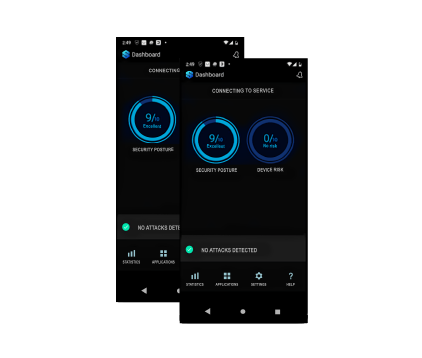
A 360 o enterprise mobile security platform: centralized management console + secure messaging & calls app to keep your trade secrets safe.

Cloud-based or On-premise Implementation Based on your organization’s needs and regulations, feel free to decide where your Sentinel Mobile Security Platform will reside: in the cloud or on premise. Whatever your decisions is we will make sure your data won’t go adrift or be threatened by hackers.

Seamless Integration Based on your organization’s needs and regulations, feel free to decide where your Sentinel Mobile Security Platform will reside: in the cloud or on premise. Whatever your decisions is we will make sure your data won’t go adrift or be threatened by hackers.
Customizable Modular Solution A 360° mobile security platform: centralized management console + secure messaging & calls app. Choose what fits your needs the best, integrate 1 solution, or take it all.
HOW IT WORKS Control the Data. Manage & Handle Risks Your Way

SaaS Implementation
Sentinel will provide

Secure Communications Apps
to be used in your organization’s software as a service structure

Supporting Infrastructure
configured to serve the requirements according to the project scope

Software Licenses
necessary to implement end-to-end encryption of your private and business communications

Configuration & Support
required to set up the infrastructure based on the project scope

System Connectivity & Hosting Services
needed to integrate the solution. The supporting infrastructure is managed and owned by Sentinel.

On Premises Implementation
Sentinel will provide for setup in 1 physical location of your choice

Secure Communications Platform
Will be installed and set up on the customer’s premises

Software Infrastructure Configuration
required to meet the scope of project implementation and deliverables

Deployment Instructions
Needed to connect the security system to the hardware infrastructure (provided & owned by the customer)

Modification, Installation, Configuration
Will be installed and set up on the customer’s premises

Secure Voice Communication Infrastructure
setup: servers to cover secured communications across a network of up to the number of devices and concurrent sessions purchased

Secured Data Gateway
setup: to cover data based communications across a network of up to the number of devices and concurrent sessions purchased
WHAT IT DOES
Protect Business Environment. Control Security Posture

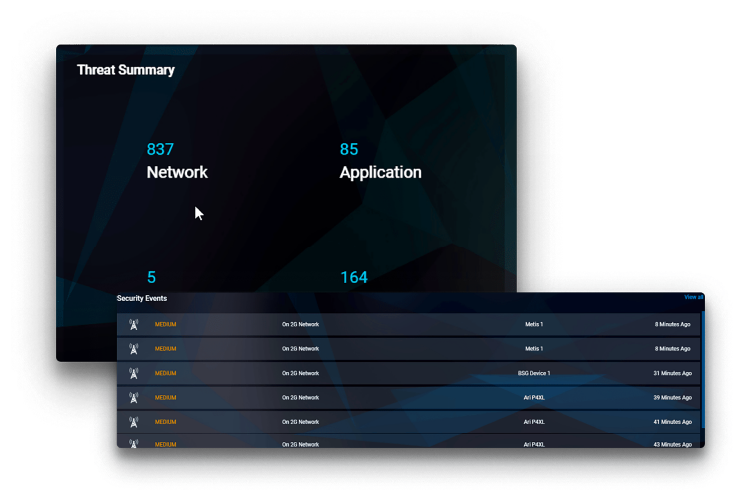
Reporting
Robust incident and activity reporting system

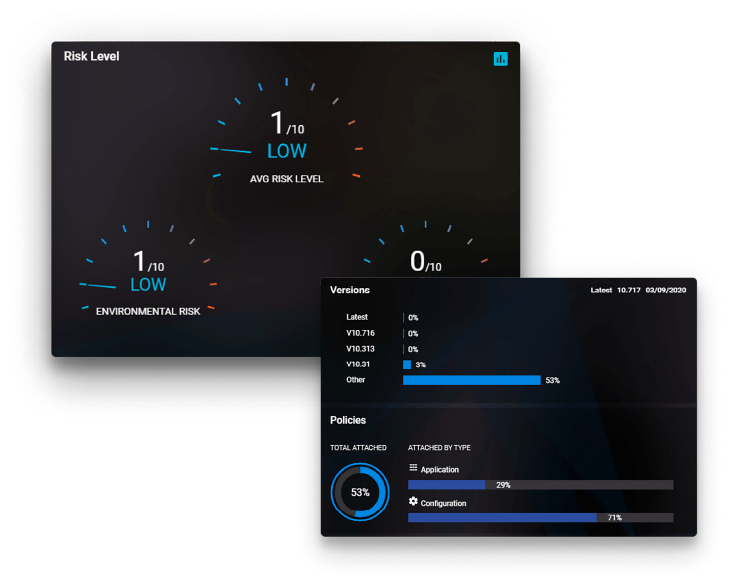
Secure OS Updates Management
Full access to devices’ life-cycle management including secure native OS software updates

Real-time Risk Level Monitoring
Groups & org. level security and posture monitoring

Centralized Visibility & Control
Organization wide security policies management
360o Smart Modular Solution
Choose what fits your needs the best. Integrate 1 solution, or take it all.
Focusing on the needs of
The convenience of mobility and digitalization has brought the threat of identity theft, supply chain attacks, trojan horses, synthetic fraud, and a lot more to critical sectors of economies and governments. Sentinel stands strong against these threats for you and your clients.

Financial Sector:
Hedge Funds &
Financial Consulting

Financial Sector:
Hedge Funds & Financial Consulting

Energy sector

Banking