SENTINEL SMARTPHONE
Fully Encrypted Smartphone
100% secure and usable. Protect your data and keep your favorite apps.

Custom built OS on high-end devices

Application security

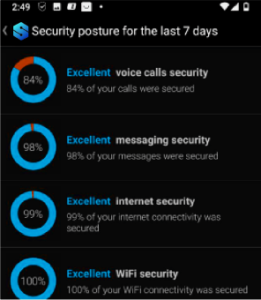
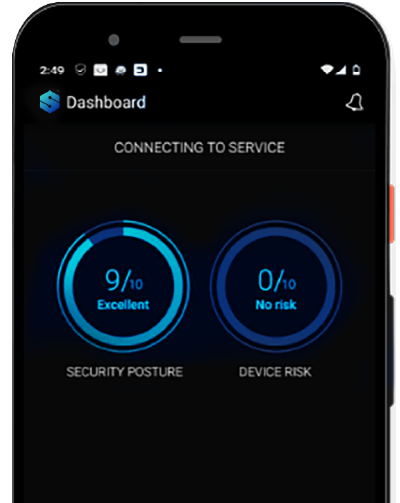
Real time risk level monitoring

Premium usability
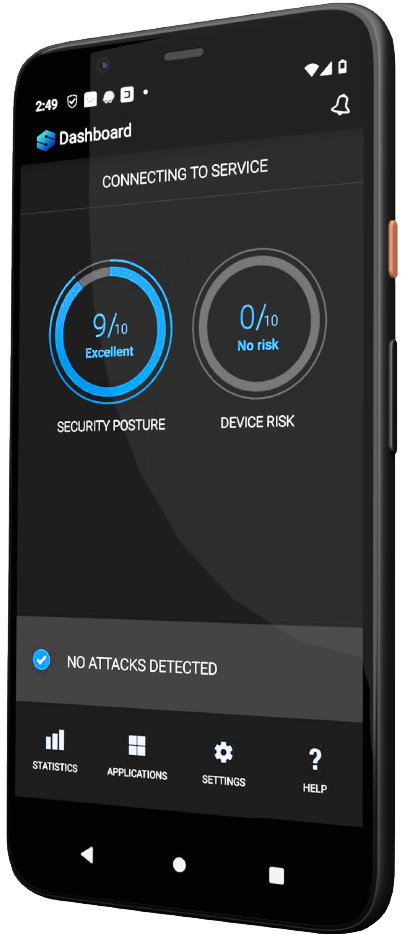

On-device management

Detection & mitigation

Personal security + emergency recording

Advanced risk resolution
Premium security on your smartphone
Over 5 billion people worldwide perform their daily personal and business activities on mobile. Mobile security hasn’t always been a top priority for Enterprises and business owners, therefore a growing number of poorly protected enterprise mobile networks and devices has become an easy target for cyber criminals.
206 time
206 time It takes 206 days to identify a data breach
$32M money
It costs $32M on average for a business to recover

Premium security on your smartphone
Over 5 billion people worldwide perform their daily personal and business activities on mobile. Mobile security hasn’t always been a top priority for Enterprises and business owners, therefore a growing number of poorly protected enterprise mobile networks and devices has become an easy target for cyber criminals.
206 time
206 time It takes 206 days to identify a data breach
$32M money
It costs $32M on average for a business to recover

The Threats

End-to-end encryption

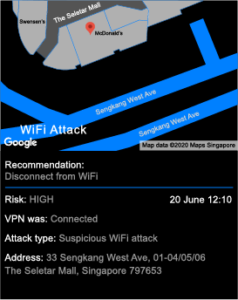
Security alert system

Hashing personal data

Ransomware

Network spoofing

Phishing
Privacy First
Prevent damaging cyber attacks from harming your organization. Kaymera continuously protects your location, voice calls, messages, and files.